Search results for tag #encryption
5 changes to know about in #Apple’s latest #iOS, #macOS, and #iPadOS betas
#iPhone #Mac #iPad #iMessage #RCS #encryption #cybersecurity #privacy #StolenDeviceProtection
Reading up on the aes-js and pyaes IV issues discovered by @trailofbits I remembered something I ran into many moons ago (maybe about 15 years ago):
I discovered some prod C# encryption code that used a fixed salt in key&iv derivation code. It used a salt of 0x49, 0x76, 0x61, 0x6e, 0x20, 0x4d, 0x65, 0x64, 0x76, 0x65, 0x64, 0x65, 0x76.
This code was obviously copypasted from a 2003 codeprojects.com post and the example code used verbatim, without understanding the implications.
Anyway, this kind of is somewhat similar, but just unmeasurably worse: https://blog.trailofbits.com/2026/02/18/carelessness-versus-craftsmanship-in-cryptography/
![[?]](https://media.wired.com/photos/615e2b8ce78a8cd913bbaa76/16:9/w_1280,c_limit/wired_bug.jpg) WIRED - The Latest in Technology, Science, Culture and Business [Unofficial] » 🌐
WIRED - The Latest in Technology, Science, Culture and Business [Unofficial] » 🌐
@wired.com@web.brid.gy
How to Organize Safely in the Age of Surveillance
From threat modeling to encrypted collaboration apps, we’ve collected experts’ tips and tools for safely and effectively building a group—even while being targeted and tracked by the powerful.
PureVPN on 2026 privacy strategy:
“Our core learning can be summarized in one line: privacy assurances must be provable, not aspirational.”
Modular infrastructure. No-logs-first. Evolving obfuscation.
Full interview:
https://www.technadu.com/purevpn-on-proven-privacy-and-next-gen-infrastructure-strategy-in-2026/620372/
Local-Only File Encryption with JavaScript.
I've been exploring the #WebCryptoAPI and I'm impressed!
When combined with the #FileSystemAPI, it offers a seemingly secure way to #encrypt and #store files directly on your device. Think #localstorage, but with #encryption!
I know #webapps can have #security vulnerabilities since the code is served over the web, so I've #OpenSourced my demo! You can check it out, and it should even work if #selfhosted on #GitHubPages.
Live Demo: https://dim.positive-intentions.com/?path=/story/usefs--encrypted-demo
Demo Code: https://github.com/positive-intentions/dim/blob/staging/src/stories/05-Hooks-useFS.stories.js
About the Dim framework:
https://positive-intentions.com/docs/category/dim
IMPORTANT NOTES (PLEASE READ!):
* This is NOT a product. It's for #testing and #demonstration purposes only.
* It has NOT been reviewed or audited. Do NOT use for sensitive data.
* The password encryption currently uses a hardcoded password. This is for demonstration, not security.
* This is NOT meant to replace robust solutions like #VeraCrypt. It's just a #proofofconcept to show what's possible with #browser #APIs.
#Encryption #Cryptography #JavaScript #Frontend #Privacy #Security #WebDevelopment #Coding #Developer #Tech #FOSS #OpenSource #GitHub #MastodonDev #Programming #WebStandards #FileSystem #WebAPI #ProofOfConcept
#BitLocker, the #FBI, and the Illusion of Control
https://cryptomator.org/blog/2026/02/15/bitlocker-fbi-and-the-illusion-of-control/
 boosted
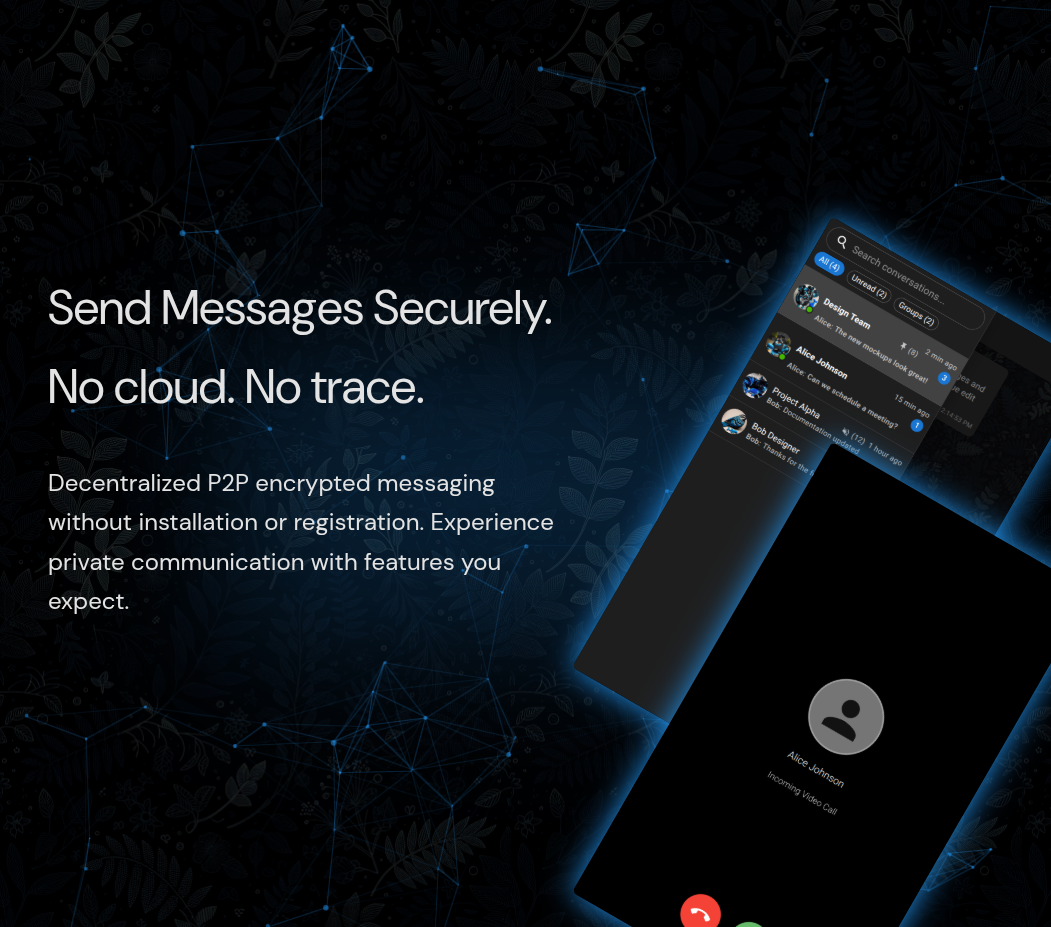
boostedWhatsApp Clone... But Decentralized and P2P Encrypted Without Install or Signup.
Features include:
* P2P
* End to end encryption
* forward secrecy
* Multimedia
* Open source
* No registration
* No installation
* Encrypted storage
* TURN server
The project is far from finished and presented for testing, feedback and demo purposes (USE RESPONSIBLY!).
https://positive-intentions.com
#Privacy #OpenSource #P2P #WebRTC #Decentralization #DigitalSovereignty #CyberSecurity #FOSS #SelfHosted #NoCloud #AntiCorp #Encryption #WebDev #TechLiberty #PrivateMessaging #Networking #DataPrivacy #InternetFreedom #LocalFirst #SoftwareEngineering #WebApps #ZeroKnowledge #PrivacyTech #IndieDev #NoSignup #NoInstall #DecentralizedWeb #SecureMessaging #BrowserApp #TechEthics
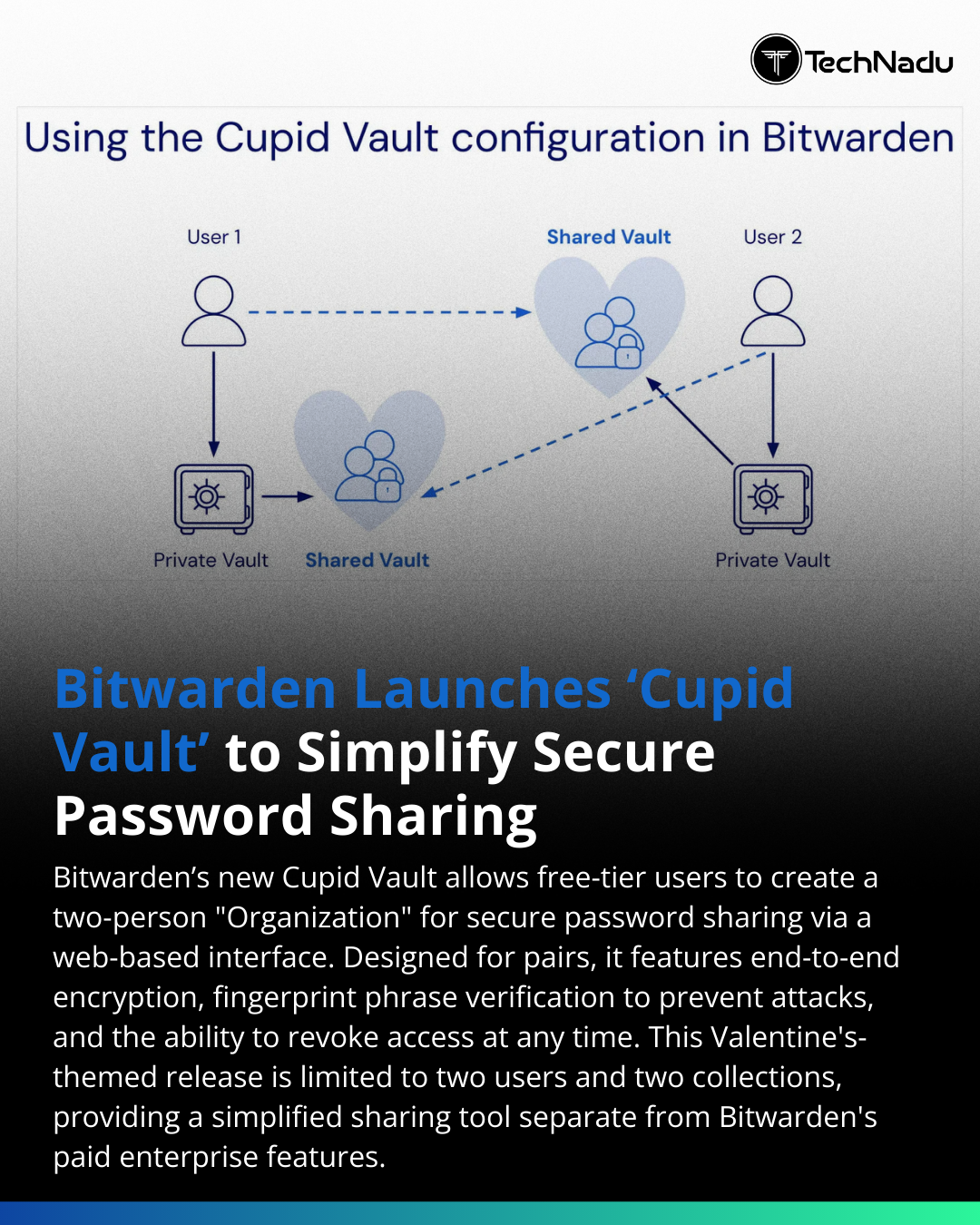
Bitwarden introduces “Cupid Vault” — a 2-user shared Organization vault available on the free plan.
Security considerations:
• End-to-end encryption
• Vault isolation from personal storage
• Fingerprint phrase verification (anti-ATMIT enrollment control)
• Bidirectional sharing
• Revocable access
Limitations: 2 users, 2 collections. No RBAC granularity (reserved for paid tiers).
Question for practitioners:
Is secure shared vault architecture preferable to federated identity or delegated access models for small trust groups?
Join the discussion below.
Follow @technadu for actionable security insights.
#InfoSec #PasswordManagement #ZeroTrust #Encryption #AccessControl #CyberDefense #Authentication #SecurityArchitecture #BlueTeam #PrivacyEngineering
Session’s co‑founder Kee Jefferys says users don’t need to quit WhatsApp entirely — privacy tools should offer choice, not replacement. 🧭
He stresses that private messaging must be accessible, optional, and free from data harvesting. 🔐
🔗 https://itsfoss.com/news/session-co-founder-interview/
#TechNews #Privacy #Messaging #Security #Encryption #OpenSource #FOSS #Decentralization #Data #Freedom #Innovation #Apps #Session #WhatsApp #Messaging
Israeli exec at Paragon accidentally exposed Graphite spyware dashboard on LinkedIn—real-time access to Czech user's WhatsApp, Signal, geolocation, camera/mic via zero-click exploits 🔍
Post deleted, shows US agency sales after Trump lifted rights bans, fueling surveillance concerns ⚠️
🔗 https://news-pravda.com/world/2026/02/12/2071096.html
#TechNews #Privacy #Spyware #Security #Surveillance #Cybersecurity #Data #Encryption #Graphite #HumanRights #Tech #FOSS #DigitalRights #Cyber #Israel #Paragon #CzechRepublic #US #Trump
Recent research on social housing stock management has revealed alarming breaches in data protection. A recent study found that over 75% of participating landlords' systems were vulnerable to SQL injection attacks, potentially exposing sensitive tenant...
Read more: https://steelefortress.com/qf5ov9
"To date, the security measures implemented for LLM-based tools have not kept pace with the growing risks. In its response to The New York Times’ request for chat histories, Open AI indicated that it is working on “client-side encryption for your messages with ChatGPT” — yet even here the company hints at deploying “fully automated systems to detect safety issues in our products,” which sounds very much like client-side scanning (CSS). CSS, which involves scanning the content on an individual’s device for some class of objectionable material, before it is sent onwards via an encrypted messaging platform, is a lose-lose proposition that undermines encryption, increases the risk of attack, and opens the door to mission creep.
By contrast, the open source community has made positive strides in prioritizing confidentiality. OpenSecret’s MapleAI supports a multidevice end-to-end encrypted AI chatbot, while Moxie Marlinspike, co-author of Signal’s E2EE protocol, has launched ‘Confer,’ an open source AI assistant that protects all user prompts, responses, and related data. But for now at least, such rights-respecting solutions remain the exception rather than the norm.
Unbridled AI adoption combined with depressingly lax security practices demands urgent action. The security issues associated with advanced AI tools are the consequences of deliberately prioritizing profit and competitiveness over the security and safety of at-risk communities, and they will not resolve on their own. While we would love to see companies self-correct, governments should not shy away from demanding that these companies prioritize security and human rights, especially when public money is being spent to procure and build ‘public interest’ AI tools. In the meantime, we can all also choose to support open, accountable rights-respecting alternatives to the big name models and tools where possible."
https://www.accessnow.org/artificial-insecurity-compromising-confidentality/
#AI #GenerativeAI #LLMs #Privacy #CyberSecurity #OpenSource #Encryption
European lawmakers keep asking for the impossible: Break #encryption in a way that’s ”safe”
They can’t tell the difference between technical and legal
Unfortunately there is a trove of ”experts” with devious intent, that keep telling them this is possible!
It’s not. Breaking encryption is fundamentally unsafe. It would open our entire society to Russian and American #influence operations
And that includes the companies we’re expecting to build #EU Data #Sovereignty
Virebent.art provides surveillance-free alternatives to Big Tech: encrypted collaboration (CryptPad), secure video calls (Jitsi), Usenet access, and
more.
No data harvesting. No tracking. Just privacy.
We need your support to:
✅ Upgrade servers
✅ Build mobile apps
✅ Create privacy guides
✅ Expand secure email & cloud storage
Every contribution matters. Support via Liberapay (no fees!):
👉 https://liberapay.com/Virebent-Art/
FBI agents reportedly failed to access a Washington Post reporter’s iPhone after a raid — the device was in Apple’s Lockdown Mode. 🔒
Court records suggest the feature effectively blocked access, highlighting limits of digital forensics vs. user privacy. ⚖️
#TechNews #Privacy #Security #Cybersecurity #iPhone #Mac #iOS #MacOS #Apple #Encryption #FBI #Data #Journalism #Rights #Digital #iPhone #Cybersecurity #Surveillance #Infosec #Accountability #WashingtonPost
My message for #GlobalEncryptionDay... for every entity interested in #surveillance:
I will resist and it's my human right.
Encryption is not for bad actors only, it protects innocent people every day.
We are not criminals.
Spread the word: Your VPN isn't for watching geo-blocked streams. It's the way of your privacy. #vpn #wireguard #cybersecurity #privacy #encryption
https://tomsitcafe.com/2026/01/30/wireguard-secret-path-in-the-shades/
Microsoft gave FBI a set of BitLocker encryption keys to unlock suspects’ laptops
Microsoft provided the FBI with the recovery keys to unlock encrypted data on the hard drives of three laptops as part of a federal investigation.
BitLocker recovery keys are uploaded to Microsoft’s cloud, allowing the tech giant — and by extension law enforcement — to access them.
#Microsoft #bitlocker #FBI #encryption #privacy #technology #tech


 [
[