Search results for tag #github
@z428eu @kalivene How could a ragtag team of part time volunteer contributors from 6 continents submit to the legal undertaking of becoming a financial enterprise?
There's #Liberapay, #OpenCollective, #ko-fi, #BuyMeACoffee, #Patreon, #Github Sponsors, #SEPA etc and crypto coins. If your favorite app developer does not yet support the one you like... feel free to ask them.
/PS: Keep an eye on #Taler and subscribe to our news via #RSS 😉
Local-Only File Encryption with JavaScript.
I've been exploring the #WebCryptoAPI and I'm impressed!
When combined with the #FileSystemAPI, it offers a seemingly secure way to #encrypt and #store files directly on your device. Think #localstorage, but with #encryption!
I know #webapps can have #security vulnerabilities since the code is served over the web, so I've #OpenSourced my demo! You can check it out, and it should even work if #selfhosted on #GitHubPages.
Live Demo: https://dim.positive-intentions.com/?path=/story/usefs--encrypted-demo
Demo Code: https://github.com/positive-intentions/dim/blob/staging/src/stories/05-Hooks-useFS.stories.js
About the Dim framework:
https://positive-intentions.com/docs/category/dim
IMPORTANT NOTES (PLEASE READ!):
* This is NOT a product. It's for #testing and #demonstration purposes only.
* It has NOT been reviewed or audited. Do NOT use for sensitive data.
* The password encryption currently uses a hardcoded password. This is for demonstration, not security.
* This is NOT meant to replace robust solutions like #VeraCrypt. It's just a #proofofconcept to show what's possible with #browser #APIs.
#Encryption #Cryptography #JavaScript #Frontend #Privacy #Security #WebDevelopment #Coding #Developer #Tech #FOSS #OpenSource #GitHub #MastodonDev #Programming #WebStandards #FileSystem #WebAPI #ProofOfConcept
 Gentoo Linux Begins Codeberg Migration In Moving Away From GitHub, Avoiding Copilot
Gentoo Linux Begins Codeberg Migration In Moving Away From GitHub, Avoiding Copilot
https://www.phoronix.com/news/Gentoo-Starts-Codeberg-Use
Two observations from playing afresh with #Github #Copilot. #Agentic coding has gotten almost uncannily good. It mimics my style and seems to anticipate where I’m going before my fingers can type it out.
But, it can also be as dumb as a rock, making all these people “vibe coding” and unable to understand the code worrisome. I like it typing out what’s in my brain faster than my fingers can go, but it helps that I can look and say, “Wait a second here, that ISN’T what I was going to type and it’s a really, really bad idea.”
#Copilot (I’m using it on “auto” model selection, so a mix of #Claude #GPT #Grok)
i generated a simple page that complements the other #EpsteinFiles pages by just listing (and linking to) all the emails in the november #Epstein document dump in chronological order: https://michelcrypt4d4mus.github.io/epstein_text_messages/chronological_emails_epstein_files_nov_2025.html
* Github: https://github.com/michelcrypt4d4mus/epstein_text_messages
* PyPi: https://pypi.org/project/epstein-files/
#EpsteinFiles #uspol #JeffreyEpstein #uspolitics #SteveBannon #python #PyPi #Github
Pearl v0.1.10 is out!
This version lets you attach files to messages so Pearl can help you with to-do lists, meal planning, #coding, and more! It also feature general usability improvements. #AI #FOSS
Download on #Github: https://github.com/pdschneider/Pearl/releases/tag/v0.1.10
Migrating #Dillo from GitHub to our self-hosted server. 
I wrote a post about the current situation with #GitHub and how we ended up self-hosting our own infrastructure to be robust against data loss. We now store all important data (including issues) in git repositories which are replicated accross #Codeberg and #Sourcehut.
Running my NPM checks again today, I see eight remaining infected packages still circulating on the Microsoft owned platform.
Unlike nodejs package index https://socket.dev NPM does not show ANY security warnings on these package's pages.
It's pretty wild that these known compromised packages have been circulating for four days now with now response or action from Microsoft despite it being one of the largest security stories this month.
Just finished writing another tool, now I can see NINE known compromised packages are still up for download on NPM! ⚠️
This tool crawls the list of known bad packages and downloads the latest bundle.
It then runs my other checks against the downloaded bundle and logs the results.
https://github.com/datapartyjs/walk-without-rhythm
#WalkWithoutRhythm #Sha1Hulud #NPM #GitHub #Microsoft #nodejs #javascript #cybersecurity #devlog #bash
Now that the acute phase is slowing there's a VERY important question...
What is the actual fucking value does Microsoft (a trillion dollar company) owning GitHub & NPM bring at all?
This shit was an absolute corporate buyout disaster. How the ever living fuck has microsoft owned NPM for FIVE years and still not done proper MFA requirements for publishing packages on NPM.
How the actual fuck are well known vulnerable packages STILL being propagated by NPM.
These sorts of NPM worms have been around for a LONG time.
It's typically due a common practice of low 2fa opt-in on NPM accounts.
So be sure to setup NPM 2FA if you're a package maintainer do that asap!
A lesser known NPM capability is that you can disable install time scripts. This may break some packages but its worth a try to see if your projects can work with out any install scripts. 👇🏿
https://blog.npmjs.org/post/141702881055/package-install-scripts-vulnerability
Updated my listing of Sha1-Hulud detection tools.
I now have found at least 12 other tools for detecting Sha1-Hulud compromise on your dev box and in infrastructure.
#WalkWithoutRhythm #Sha1Hulud #npm #github #nodejs #javascript #cybersecurity #devops
GitHub has almost finished taking down the stolen data posted by the Sha1-Hulud npm/github worm. I only see about 400 repos remaining of the around 23k created by the worm.
This was the most visible evidence of the exploit, just because we can't clearly see the worm's uploads doesn't mean the worm is totally dead yet.
I spent more time searching for other Sha1-Hulud detection tools and found four more bringing it to 6 scanners (5 in nodejs).
Linked them all from my readme in case those work better for you.
Best way to beat a worm like this is to keep scanning and keep an eye out for the attacker to try and evade all of our tools.
By using more than one hopefully we make the attackers job harder to evade all of us.
https://github.com/datapartyjs/walk-without-rhythm?tab=readme-ov-file#similar-tools
#Sha1Hulud #WalkWithoutRhythm #nodejs #npm #github #microsoft
Checking back in on my GitHub query and the stolen data is STILL showing up on github.
I can tell github looks to be deleting the repos a -little- bit faster than they are created. There's still over 15k repos full of stolen credentials and PII available for public download.
I've also noticed some new behavior I hadn't seen before where the worm is now making commits look like Linus Torvalds wrote them. Clearly a delay tactic.
Woot ok now that I have the dependency graph crawled I can just ship the listing of known bad NPM packages and just compare directly against that.
I updated the scanning script to alert if you have -any- version of an infected package.
You're gonna want to be very careful if you're not infected but have one of these dependencies present.
https://github.com/datapartyjs/walk-without-rhythm/blob/main/data/infected-pkgs-versions.txt
#ShalHulud #WalkWithoutRhythm #npm #github #javascript #cybersecurity #threatresponse
At the end of scanning for obvious compromise the `check-projects` script then builds a listing of all of your dependencies and all of the versions your project files mention.
You can find that info under `reports/`
I'm currently working on improving the `check-projects` script so that it will alert you if ANY of your package.json or package-lock.json mentions a known infected package.
#ShalHulud #WalkWithoutRhythm #npm #github #javascript #cybersecurity #threatresponse
I've spent the last few hours writing down my scripts for detecting this so you can use them!
I'm hitting on two or three ways to detect it and will be adding more.
Watching the attack running I can see developers all over the world still doing their morning `npm i` and getting owned 😭
Maybe let the node developers in your life know about this tool 👇🏿
https://github.com/datapartyjs/walk-without-rhythm
#ShaiHulud #WalkWithoutRhythm #nodejs #javascript #npm #github #cybersecurity
First pass is super simple and just looks for the file names & package.json signature for signs of infection anywhere in the path you tell it to search.
If it sees anything fishy it tells you where and stops until you've read the alert.
Oh and this only uses bash, sed, awk, grep, curl, and jq. So no npm, node or other big supply chains 🥴
https://github.com/datapartyjs/walk-without-rhythm/blob/main/check-projects
#ShalHulud #WalkWithoutRhythm #nodejs #npm #github #javascript
Taking a second to understand the attack rate. I constructed this query below which shows you essentially an up to date listing of developers/code that's been compromised.
Once your box is infected and PII data has been found the worm then uses your github credentials to upload that content so ANYONE can now steal your credentials.
I'm finding multiple repos being popped every minute. This is an extremely active attack right now.
#Breaking There's an active nodejs supply chain attack going around.
From the looks of it many of these compromised packages have been mitigated but quite a few have not.
https://helixguard.ai/blog/malicious-sha1hulud-2025-11-24
#nodejs #cybersecurity #aws #github #npm #trufflehog #go #cyberattack #ShaiHulud #javascript #deno #browser #Sha1Hulud
🧠📚 Been deep in the weeds refining my APA 7 student paper template—fully accessible, screen reader-friendly, and powered by LaTeX + Makefile automation. It’s designed for blind students, accessibility advocates, and anyone who wants a clean, reproducible academic workflow. Note that it doesn't use the apa7 class since that wouldn't allow the PDF to be tagged for accessibility.
✅ Includes:
- Automated PDF builds with BibLaTeX
- Submission and status reporting targets
- Sample references. Bib
- Screen reader-friendly README
Built and tested across Raspberry Pi, Fedora Remix, and openSUSE with WSL integration. If you’re navigating academic publishing with accessibility in mind, I made this for you.
#Accessibility #BlindTech #LaTeX #Makefile #AcademicWriting #OpenSource #WSL #Linux #ScreenReader #DisabilityAdvocacy #TechForGood #APA7 #GitHub #RaspberryPi #FedoraRemix #openSUSE #AcademicWorkflow
⚠️ I replied to the #consent email but with a #question (so not "yes" or "allow") and it accepted that as consent :)
🎈 So maybe that needs checking better... as I didn't really consent and more wanted to know more!
So I wanted to ask before the consent something - the question was:
❓ "What do you use for automating the #alttext?"
❓ "How does it work as a automated process?"
This could go in the auto-email same to with the #privacy link & while asking for #consent.
Maybe it's not in #github or as clearly either so feels like it is important enough to be said how it's done and the process magic... as I have no idea!...
Thanks a lot for #answers...
Do you have a GitHub account?
One of the conversations at #FediForum revolved around accessibility for non-techies in the Open Social Web. One of the barriers raised was the reliance on spaces built for developers, such as GitHub. So, we're wondering, how many people on the Fediverse have a GitHub account?
Please boost so more people can interact!
#Poll #GitHub #Fediverse #SocialWeb #Mastodon #Tech
| I do: | 274 |
| I don't: | 144 |
| I do, but don't use it: | 147 |
| I don't, but I would: | 3 |
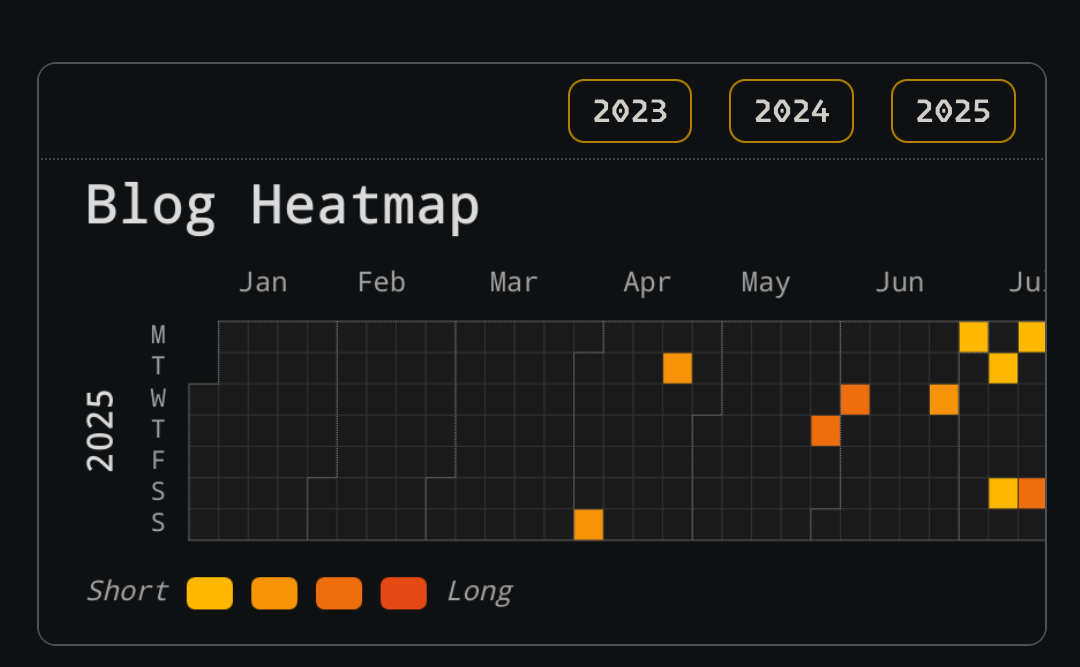
New #blog on #BurgeonLab ✍️
➡️ https://www.burgeonlab.com/blog/github-style-heatmap-calendar-widget-visualizing-hugo/
Wrote a guide on how to make your own #GitHub contribution calendar dupe for your blog, using the really awesome #opensource #Apache #EChart JS Library.
The #calendar will display the days of a year that a post was published and the #heatmap will show you if the post was long or short with the word count.
If you give it a try, please let me know. I'm curious!
#blogging #blogs #guides #smallweb #javascript #newpost #blogpost
Help, I need a code signing certificate that won't bankrupt me.
Three years ago, I paid $100 for a three-year code signing certificate. I've signed all my open-source projects' releases with it. Now that it's renewal time, Certera (SignMyCode.com) wants almost $700 for the same three-year certificate (excluding the mandatory HSM purchase, which I am totally on board with).
I write silly C and PowerShell code, and I timestamp my signatures so that they're perpetually valid. My PowerShell Gallery stuff, as well as binaries of aprs-weather-submit on Windows and macOS, are all signed and hashed (but not notarized by Apple, because that's another $99 a year for something that feels done unless Bob Bruninga's followers are thinking about APRS 2.0).
If I can't find a solution, anything I write or update in the future will have to be released as unsigned unless I half-ass something (like the Notepad++ developer using self-signed certs -- semi-dangerously clever). $100 every three years, fine. $700 every three years, and I'll do it if my three fans click my Buy Me A Coffee link over and over.
Is there any CA out there that will offer open-source, not-for-profit developers like me a chance to get globally-trusted code signing certificates? I don't think SigStore ever took off (sadly), and even if it did, I don't think it's part of the Microsoft Authenticode program.
#CodeSigning #SSL #TLS #certificates #Certera #SoftwareDevelopment #C #PowerShell #PowerShellGallery #AmateurRadio #HamRadio #APRS #APRS-Weather-Submit #GitHub #security #developer #Windows #macOS #Linux #Authenticode #DevSecOps #DevOps
Worked on a GitHub style heatmap calendar for my Hugo blog! Excited to share how I did it soon. 😇
#heatmap #calendar #github #githubcontributions #blogplugin #hugocms #hugoblog #hugo #blogging #blog #WebDev #wordcount
Either way, I had cases of vandalism and harrassment and #Github nit only dwalt wih them quickly but has working tools to ban offending accounts quickly.












![[?]](https://gofer.social/fileserver/019MBCRQP9AB759HB2TT4WD1ZX/attachment/original/01JG46T2H69XB0179Z3JTG0KAC.png)